TL;DR:
- Encryption is essential for high-risk banking sectors but requires a layered approach including proper key management and controls. Regulatory frameworks like GLBA, PCI DSS, and EPC set strict standards for encryption practices, emphasizing detailed policies and regular audits. Effective security depends not only on algorithms but on architecture, policies, and layered defenses to prevent breaches and ensure compliance.
Encryption sits at the heart of every serious banking security conversation, yet it remains one of the most misunderstood controls in crypto, fintech, and iGaming operations. Many operators assume that switching on encryption is equivalent to building a fortress, only to discover that data breaches remain frequent and costly, and that ransomware can bypass even well-implemented encryption when attackers gain access to keys or compromise endpoints. This guide cuts through the noise and addresses what encryption actually does, what the regulations demand, and how to build the layered architecture that genuinely protects your banking operations.
Key Takeaways
| Point | Details |
|---|---|
| Encryption is essential | Banks and high-risk businesses must use encryption, but it works best when layered with other cybersecurity controls. |
| Compliance is non-negotiable | Major regulations explicitly require robust encryption methods for banking data in transit and at rest. |
| Key management matters most | Even the strongest encryption fails without secure, well-governed key management policies and tools. |
| Layered security is necessary | Real protection comes from combining encryption with monitoring, IAM, and endpoint defences. |
Why encryption is critical for banking in high-risk industries
High-risk sectors operate with unusually attractive targets on their backs. Crypto exchanges hold digital assets worth millions. iGaming platforms process thousands of card transactions per hour. Fintech providers bridge traditional banking with emerging payment rails. Every one of these touchpoints is a potential breach vector, and the financial and reputational consequences of a compromised database are severe.
The temptation is to treat encryption as a silver bullet. It is not. According to Results Technology, encryption functions as both a preventive control (protecting confidentiality against unauthorised access) and a detective control (revealing tampering or alterations when paired with integrity mechanisms). That dual role is powerful, but only when encryption is implemented as part of a defence-in-depth strategy rather than as a standalone fix.
“Encryption implemented in isolation is like a bank vault with no lock on the front door. The steel is impressive, but the architecture is fatally flawed.”
Consider what a breach scenario looks like for a crypto exchange. An attacker does not need to crack AES-256. Instead, they compromise a developer’s credentials, move laterally through the infrastructure, and export encrypted data alongside the decryption keys stored carelessly on the same server. The encryption was technically sound. The architecture was not.
For high-risk businesses pursuing banking security compliance, the lesson is consistent: encryption creates the conditions for security, but controls around access, monitoring, and key custody determine whether those conditions hold. Operators in secure crypto operations will recognise this challenge immediately.
Key reasons why encryption remains mandatory despite its limits:
- Regulatory bodies across the EU and US treat encryption as a baseline, non-negotiable safeguard.
- Banks and EMIs require demonstrated encryption controls before onboarding high-risk merchants.
- Breach disclosure laws in most jurisdictions offer safe harbours only when encrypted data is confirmed unreadable.
- Insurance underwriters increasingly price cyber policies based on encryption maturity.
Regulatory expectations: Encryption in banking compliance frameworks
Understanding what regulators actually require removes a lot of guesswork. Three frameworks are most relevant to high-risk sector businesses operating with banking partners across the US and EU.
GLBA (Gramm-Leach-Bliley Act): Under US financial-sector obligations, the GLBA Safeguards Rule treats encryption as an important safeguard within a written information security programme. Financial institutions and their service providers must encrypt customer information both in transit and at rest.
PCI DSS v4.0: For any operator handling payment card data, PCI DSS v4.0 requirements are explicit: cardholder data must be protected with strong cryptography during transmission and rendered unreadable in storage, with specific emphasis that disk-level encryption alone does not satisfy the requirement. Database, table, and file-level controls are expected.
European Payments Council (EPC): The EPC’s annual cryptographic guidelines cover algorithm selection, key management practices, authenticated encryption, and even forward-looking approaches like homomorphic encryption. These guidelines carry real weight with EU-based banking partners.
| Framework | Scope | Key encryption requirement | Key management focus |
|---|---|---|---|
| GLBA | US financial institutions and service providers | Encryption of customer data in transit and at rest | Written information security programme |
| PCI DSS v4.0 | Payment card processing environments | Strong cryptography in transit; unreadable stored cardholder data beyond disk-level | Key rotation, access controls, monitoring |
| EPC guidelines | EU payments ecosystem | Authenticated encryption; algorithm currency | Advanced key management, homomorphic encryption |
The numbered steps for achieving compliance alignment across all three frameworks are:
- Conduct a data inventory to identify all customer and payment data flows.
- Map each data category to the applicable regulatory framework.
- Apply the highest applicable encryption standard where frameworks overlap.
- Document your key management architecture in your written security programme.
- Commission an independent audit to validate alignment before approaching banking partners.
For businesses needing to align their payment data compliance posture, understanding these frameworks in detail before approaching EMIs or acquiring banks will meaningfully improve your approval odds.
Statistic callout: PCI DSS non-compliance is cited as a contributing factor in the majority of payment card breaches. Encryption gaps, particularly around unprotected stored cardholder data and unencrypted internal network transmissions, remain the most commonly failed controls during QSA assessments.
How encryption actually works: Methods and implementation in banking
Encryption is not one technology. It is a family of methods, each suited to different situations in a banking environment.
Symmetric encryption uses the same key to encrypt and decrypt data. It is fast and efficient, which makes it ideal for encrypting large volumes of stored data, such as transaction records or customer databases. AES-256 is the standard bearer and is accepted across all major regulatory frameworks.
Asymmetric encryption uses a public key to encrypt and a private key to decrypt. It is computationally heavier but solves the key distribution problem. TLS handshakes, for example, rely on asymmetric cryptography to establish a shared session key, after which symmetric encryption takes over for the actual data transfer.
| Method | Use case | Speed | Key complexity |
|---|---|---|---|
| AES-256 (symmetric) | Database encryption, stored files | Fast | Single shared key |
| RSA / ECC (asymmetric) | TLS handshakes, digital signatures | Slower | Public/private key pair |
| Tokenisation | Payment card data substitution | Near-instant | Vault-based lookup |
| Format-preserving encryption | PAN data in legacy systems | Moderate | Structured key management |
Protecting data in motion requires TLS 1.2 as a minimum, with TLS 1.3 strongly preferred for new deployments. VPNs add a further layer for internal traffic between distributed infrastructure nodes. Anything below TLS 1.2 should be treated as a critical vulnerability and remediated immediately.
Protecting data at rest goes beyond full-disk encryption. Regulators expect column-level or table-level database encryption for sensitive fields, file-level encryption for document stores, and tokenisation for payment card numbers where the actual PAN value does not need to be retained.
Advanced methods worth understanding:
- Authenticated encryption (AE/AEAD): Simultaneously protects confidentiality and verifies integrity. GCM mode with AES is the most widely deployed variant and is specified in EPC guidance.
- Homomorphic encryption: Allows computation on encrypted data without decrypting it first. Still emerging in production banking environments but increasingly relevant for privacy-preserving analytics.
- Format-preserving encryption (FPE): Encrypts data whilst retaining its original format, critical for legacy systems where database schemas cannot be changed.
Pro Tip: Never rely on your cloud provider’s default encryption settings. Defaults are designed for broad compatibility, not regulatory compliance. Review each setting explicitly against your applicable frameworks before going live.
Encryption for crypto banking environments demands particular attention to wallet key infrastructure and API gateway encryption, both of which have caused significant losses when poorly implemented. For reference on bank-grade encryption reliability, mature implementations combine multiple layers rather than relying on any single method.
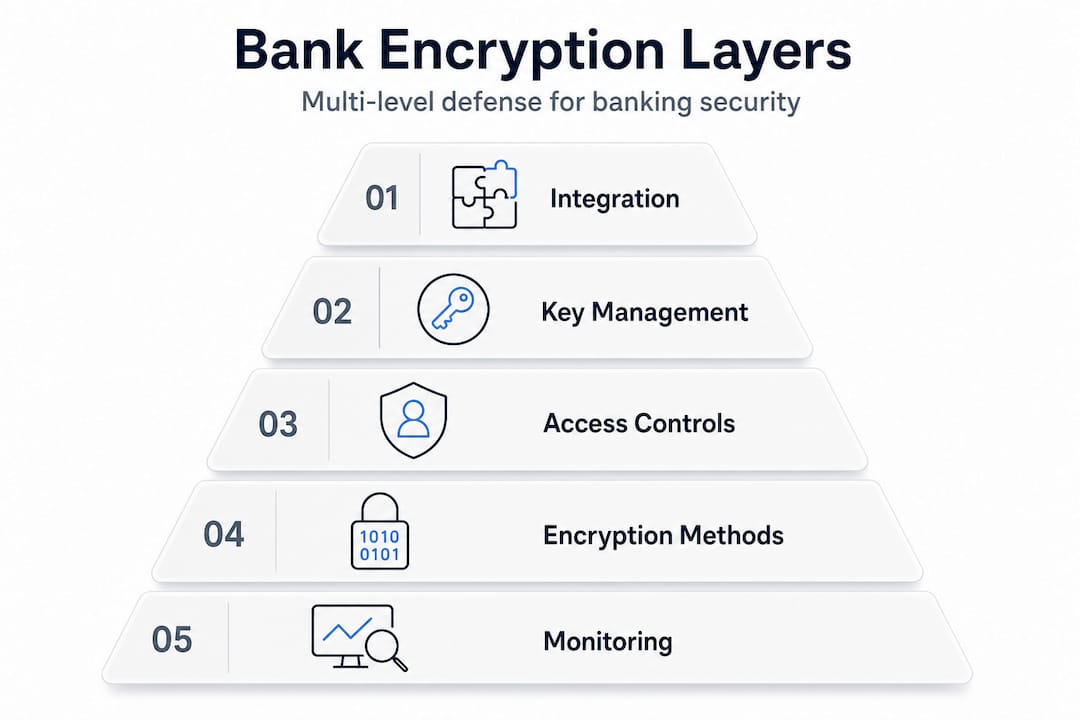
According to Results Technology, real effectiveness comes from integration with key management, access controls, and monitoring. The technology is only as strong as the processes surrounding it.
Key management: The overlooked pillar of encryption security
If encryption is the lock, key management is the locksmith. Get it wrong and even the strongest cipher becomes irrelevant.
Key management architecture is a major nuance in cloud and outsourced banking environments. When a provider can access your keys, regulatory expectations effectively shift risk onto you as the operator. This motivates the increasing adoption of customer-controlled key designs, where the bank or operator generates and stores its own keys, independent of the infrastructure provider.
The critical elements of sound key management for high-risk sectors:
- Key rotation: Cryptographic keys must be rotated on a defined schedule. Annual rotation is the common minimum; quarterly is preferable for high-value environments.
- Segregation of duties: The person who manages keys should not be the same person who manages the systems they protect. Dual-control procedures prevent insider threats.
- Hardware Security Modules (HSMs): HSMs are tamper-resistant physical devices purpose-built for key storage and cryptographic operations. They are the gold standard for key custody in banking environments.
- Auditability: Every key creation, rotation, access, and deletion event must be logged and reviewable. Regulators will ask for these records during examinations.
- Key escrow policies: Define clearly who can access keys in an emergency and under what conditions. An undocumented key recovery process becomes a crisis when you need it most.
Pro Tip: When evaluating cloud-based banking infrastructure for your crypto banking setup, always ask providers directly whether they retain any ability to access your encryption keys. If the answer is ambiguous, assume they can.
Poor key management is a recurring factor in breaches involving crypto risk management failures. Keys stored in source code repositories, hardcoded in configuration files, or accessible via shared admin accounts represent the most common and most avoidable vulnerabilities. Your crypto compliance fundamentals should include explicit key management policies reviewed by legal and technical teams together.
Why defence-in-depth matters: Layering encryption for real-world resilience
Encryption and key management are necessary but still insufficient on their own. The Verizon DBIR 2025 confirms that data breaches remain frequent and costly, and ransomware attackers have become adept at navigating around encryption by targeting the humans and processes that control keys rather than the cryptographic algorithms themselves.
“Attackers do not break encryption. They find the person or process that holds the key and compromise that instead.”
The attack surface in a high-risk banking environment extends far beyond the data layer. Endpoint devices, identity and access management (IAM) systems, API gateways, and third-party integrations all represent potential entry points. Results Technology consistently emphasises that monitoring, penetration testing, and certificate hygiene are the controls that close the gaps encryption leaves open.
A practical layered control checklist for high-risk banking environments:
- Implement TLS 1.3 for all external communications and enforce certificate pinning for mobile applications.
- Deploy a Security Information and Event Management (SIEM) system with real-time alerting on anomalous decryption events.
- Conduct penetration testing at least annually, with a specific focus on key extraction and lateral movement scenarios.
- Enforce multi-factor authentication (MFA) on all systems with access to encrypted data or key management infrastructure.
- Automate certificate renewal to eliminate expiry-related outages and man-in-the-middle exposure windows.
- Segment networks so that a compromise in one zone cannot propagate to the zone holding encryption keys or cryptographic infrastructure.
For secure data-powered banking operations, these controls are not optional enhancements. They are foundational. Operators who build comprehensive security strategies with layered controls consistently demonstrate stronger compliance postures and face fewer onboarding rejections from banking partners.
What most high-risk businesses get wrong about banking encryption
Here is the uncomfortable truth after working across crypto, iGaming, and fintech banking engagements: the algorithm is almost never the problem. Operators obsess over whether to use AES-256 or ChaCha20, debate key lengths at length, and spend months selecting a cryptographic library. Meanwhile, their decryption keys are stored in a plaintext config file on a shared developer server, and their incident response plan has not been tested in two years.
The failures we observe repeatedly fall into three categories. First, architecture decisions made for developer convenience rather than security: keys co-located with the data they protect, shared admin accounts with no audit trail, or encryption applied at the application layer but not at the database layer. Second, policy gaps where encryption exists but nobody has documented who is responsible for key rotation, how a compromised key gets revoked, or what happens when a developer with key access leaves the company. Third, the absence of verification. Many operators assume their encryption is working correctly because their vendor says so. They have never tested whether an attacker with access to their backup storage could actually read the data.
The high-risk businesses that consistently pass banking due diligence are not necessarily running the most exotic cryptographic implementations. They have clear, documented policies, regular third-party testing, and board-level visibility into their security posture. That combination impresses compliance officers far more than an impressive algorithm name in a technical brochure.
The practical advice: hire a qualified external auditor to attempt to bypass your encryption before your banking partner does it for you during due diligence. Review your crypto banking solutions breakdown not just for functionality but for the security architecture assumptions baked into each product. And treat encryption as a living programme, not a one-time implementation checkbox.
Secure your high-risk banking with expert solutions
Building encryption that satisfies regulators, impresses banking partners, and genuinely protects your operation is not a solo endeavour. At BankMyCapital, we work specifically with crypto, iGaming, fintech, and forex businesses to establish banking relationships with partners who understand your risk profile and your security requirements. Whether you are navigating your first banking rejection risks guide or restructuring your compliance posture ahead of a banking application, our network of over 50 pre-vetted partners and in-house compliance specialists can help you move faster and more confidently. Explore our crypto banking setup guide for technical onboarding guidance, or review our high-risk banking checklist to benchmark your current readiness.
Frequently asked questions
Is disk-level encryption enough for bank compliance?
No; compliance frameworks like PCI DSS and GLBA require encryption controls that exceed disk-level encryption, with PCI DSS v4.0 mandating strong cryptography for data in transit and specific protections for stored cardholder data beyond the disk layer.
What encryption standards are most accepted by banks in the EU and US?
Banks generally require compliance with standards like PCI DSS, GLBA, and EPC guidelines; GLBA expectations cover data in transit and at rest, whilst EPC guidance specifies authenticated encryption and current algorithm selection across EU payment environments.
Does encryption protect against all cyber threats in banking?
No; as the Verizon DBIR 2025 confirms, encryption cannot stop attacks where adversaries compromise endpoints or obtain keys, making layered defences and rigorous key management equally essential.
Why are key management policies critical in banking encryption?
Without strong key management, even advanced encryption can be bypassed; key management architecture determines who controls keys and how they are rotated, and poor designs that allow provider access to keys effectively transfer your security risk to a third party.